Tazeen Dhedhi
EE379K
Due:
Homework 3
1. Obtain copies of RFC 793 and 826.
Done.
2. Produce a diagram of the Transmission
Control Protocol header and describe the function of each of the fields in the
header.
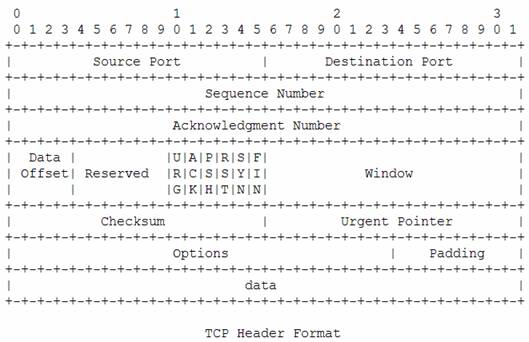
Sequence Number: If SYN is not
present, it is the sequence number of the first data octet in this packet. If
SYN is present, then it is the initial sequence number (ISN) and the sequence
number of the first data octet in this packet is ISN+1.
Acknowledgement Number: If the ACK bit is
set, then this field contains the sequence number of the next packet the sender
is expecting from the receiver. Once a connection is established, this is
always sent.
Data Offset: The length of the
TCP header in terms of 32-bit words. The length of the TCP header is always a
multiple of 32, and this field specifies where the data begins.
Reserved: These bits are
always zero. They are reserved for future use, in case the protocol has to be
extended in some way.
Control bits: 6 bits (from left
to right):
·
URG. This bit is set to show that the Urgent Pointer field
is valid.
·
ACK. This bit is set to show that the Acknowledgement Number
field is valid.
·
PSH. Push function.
·
RST. Reset the connection.
·
SYN. Synchronize sequence numbers.
·
FIN. No more data from sender
Window: The number of data octets beginning
with the one indicated in the acknowledgement field that the sender is wiling
to accept. This field is used for flow control by the sender, to indicate to
the receiver the amount of data for which it has available resources.
Checksum: The checksum field
is the 16-bit one’s complement of the one’s complement sum of the 16-bit words
in the header and text. If a segment contains an odd number of header and text
octets to be checksummed, the last octet is padded to
the right with zeros to form a 16-bit for the purpose of calculating the
checksum. The pad is not transmitted as part of the segment.
Urgent Pointer: This field
contains the value of the urgent pointer as a positive offset from the sequence
number. It points to the sequence number of the octet following the urgent
data. This field is to be considered only if the URG bit is set.
Options: These can be of any length that is
a multiple of 8 bits. There are two formats for an option:
i. A single octet of
option-kind.
ii. An octet of
option-kind, an octet of option-length, and the actual option-data octets.
|
Kind |
Length |
Meaning |
|
0 |
- |
End of option list |
|
1 |
- |
No-operation |
|
2 |
4 |
Maximum Segment Size |
|
3 |
3 |
Window Scale |
|
8 |
10 |
Timestamp |
End of
option list: This is used after all the options to indicate that there are no
more options to process.
No-operation:
This may be used between options, for example, to align the beginning of a
subsequent option on a word boundary.
Maximum
Segment Size: This option must only be sent in the initial connection request.
It specifies the maximum receive segment size at the TCP which sends this
segment. If this option is not used, any segment size is allowed.
Window
Scale: This value is used to shift the window size field's value up to a
maximum value of approximately a gigabyte. Both the sender and the receiver
must send this option in the SYN and SYN/ACK packets during the handshake, if
they are willing to use Window Scaling.
Timestamp:
This option can be used to measure the round-trip delivery time for a data
segment. It has two fields: Timestamp Value and Timestamp Echo Reply. When a
host first timestamps a packet in a connection, it puts its timestamp in the
Timestamp Value field and sets the Timestamp Echo Reply field to 0. Then when
the second host receives the packet, it copies the Timestamp Value into the
Timestamp Echo Reply field and puts its timestamp into the Timestamp Value
field.
Padding: The padding is used to ensure the
TCP header ends and the data begins on a 32-bit boundary.
3. Explain the operation of the Address
Resolution Protocol (ARP) and the role it plays in local area network
communications.
A
packet is sent down through the network layers. The Address Resolution module
tries to map the <protocol type, target protocol address> pair to a
48-bit Ethernet address. If it doesn’t find the pair, then it sends an ARP Request message using Ethernet
broadcast. Everyone receives the message. Only the target sends back an ARP Response message to the sender of
the ARP Request message.
It
allows dynamic discovery of the rest of the local area network.
4. Read chapters 4 through 6 of the text.
Book not yet available.
References
RFC 793, 1323
. Studying